A 48-hour code audit is a rapid, structured deep-dive into your software’s architecture, security posture, and technical debt. In just two days, an external audit team can surface vulnerabilities, scalability bottlenecks, and legacy code issues that your internal team has systematically missed. This article walks through exactly what gets found, why it matters, and what to do next.
There’s a particular kind of confidence that comes from having built something yourself. You know the system. You know where the bodies are buried. You’ve got mental maps of the codebase that no documentation could ever replicate. And that, ironically, is exactly the problem.
When your team has lived inside a codebase for six months — or six years — they develop blind spots. Not because they’re careless, but because familiarity breeds tolerance. That three-year-old authentication module that “works fine.” The API endpoint with no rate limiting that nobody’s touched because touching it breaks other things. The database schema that made sense in year one but is now strangling every new feature you try to ship.
A 48-hour code audit is built specifically to see what your team can’t or won’t see anymore. It’s fast, it’s focused, and the findings are often sobering. Here’s what one typically uncovers.
What Is a 48-Hour Code Audit?
A 48-hour code audit is a rapid technical assessment of a software application’s codebase, typically performed by an external team, that identifies security vulnerabilities, architectural flaws, technical debt, and scalability bottlenecks. Most audits surface critical issues in security, performance, and code maintainability — issues that internal teams often overlook due to familiarity bias, time pressure, or accumulated shortcuts taken during development.
Why Your Team Is Probably Missing More Than You Think
Let’s start with some numbers that should make you uncomfortable.
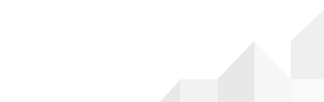
Deloitte’s 2026 Global Technology Leadership Study estimates that technical debt accounts for 21% to 40% of an organisation’s IT spending. That’s not a marginal drag; that’s nearly half your budget being quietly consumed by decisions made years ago.
Moreover, a CAST report published in September 2025, based on an analysis of more than 10 billion lines of code, found that companies and governments would need to spend 61 billion workdays in software development time to pay off the technical debt they’ve accrued over the past four decades. Even if every developer on the planet stopped building new things and focused entirely on this problem, it would take nine years to solve.
And here’s the part that stings for engineering leads: half of all software developers say technical debt lowers team morale, and research indicates it can reduce development speed by up to 30%. Your team isn’t slow because they’re not good enough. They’re slow because they’re wading through debt that never got addressed.
A software code audit doesn’t just show you what’s broken. It shows you why your team feels like they’re running in quicksand.
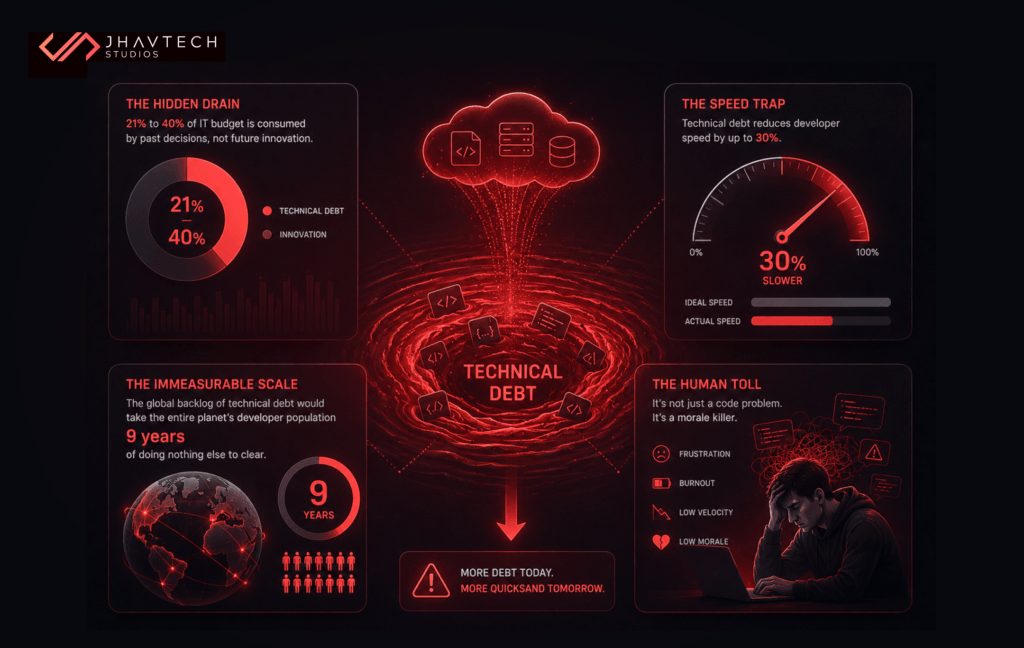
The 5 Things a 48-Hour Code Audit Almost Always Finds
1. Security Vulnerabilities Hiding in Plain Sight
This is consistently the most alarming finding, because the vulnerabilities aren’t exotic: they’re basic.
According to a 2026 audit of commercial codebases, 86% of applications evaluated contained open-source software vulnerabilities, with 81% having high- or critical-risk vulnerabilities. Additionally, 90% of audited codebases had open-source components more than four years out-of-date.
Read that again: 9 in 10 applications are running components that haven’t been patched in over four years. In cybersecurity terms, that’s not a risk; it’s an open invitation.
A proper app code review will scan every dependency, map injection points, flag hardcoded credentials (yes, they’re still being found in 2026), and check for misconfigured authentication flows. It’s not unusual to find a critical CVE sitting in a rarely-touched library that the team forgot they even imported.
The OWASP Top 10, which covers the most critical web application security risks, remains the benchmark for what auditors look for. A 2025 report by Veracode found that 45% of AI-generated code samples failed security tests and introduced OWASP Top 10 vulnerabilities into codebases. If your team has been leaning on AI coding assistants (and most teams now have), this deserves immediate attention.
2. Architectural Debt That’s Quietly Killing Scalability
You know the feeling. Everything works at 1,000 users. At 10,000, things get shaky. At 100,000, the system falls over. This is almost never a server problem. It’s almost always an architecture problem, and it’s precisely what a technical debt audit is designed to surface.
According to Gartner, 80% of technical debt will be architectural by 2026. That means the problem isn’t a few messy functions; it’s the structure of how your system was built. Monolithic services that should have been separated years ago. Synchronous calls where async processing would eliminate bottlenecks. Database queries that scan full tables instead of hitting indexes. Caching layers that were promised in sprint three and never made it in.
During a 48-hour audit, an experienced architect will draw out the actual call flow and identify exactly where your software scalability issues will emerge under load. It’s the kind of work that’s hard to justify internally because it doesn’t ship a feature. It’s easy to justify once your app crashes during a product launch.
3. Legacy Code Nobody Wants to Touch
Every codebase has them: the modules that have been around since the beginning, that everyone knows are fragile, that nobody wants to touch because touching them breaks three other things. The code that’s held together with string, duct tape, and the institutional knowledge of the one developer who built it and has since left.
A legacy code assessment doesn’t just inventory these problem areas. It evaluates their blast radius. What would happen if that service failed? What does it block? How much of the rest of the system depends on it?
Stripe’s Developer Coefficient report found that 42% of professional developer time goes to managing technical debt. That’s the equivalent of 84 hours per week for a team of five, representing a $168,000 annual productivity cost even at a modest $80,000 per person salary.
In many cases, a 48-hour audit finds that teams are spending nearly half their working week just keeping the lights on. That’s not sustainable and it’s usually invisible to leadership until someone puts a number on it.
4. Missing or Broken Test Coverage
Test coverage is one of those things that looks fine until you actually check it. You’ve got a CI pipeline. Tests run. They mostly pass. Everything must be fine. Except that the coverage report is lying to you.
There’s a meaningful difference between lines touched by a test and behaviour actually being verified. Audit teams look at branch coverage, mutation testing results, integration test gaps, and whether the critical paths through your application are actually being tested end-to-end, or just touched incidentally by tests that were never designed to catch the real failure modes.
The cost of this gap only becomes clear in production. A bug that could have been caught by a proper test costs, on average, six times more to fix after release than before. A bug found in production by a customer costs even more in engineering time, reputation, and churn.
5. Performance Bottlenecks That Are Invisible in Development
Development environments lie to you. Your local database has 500 rows. Production has 50 million. Your local API has no network latency. Your users in regional Australia have 180ms round trips to your servers.
A mobile app audit or web application audit will almost always surface N+1 query problems, unindexed foreign keys, synchronous operations that should be queued, images that are being served at full resolution and resized in the browser, and JavaScript bundles that are three times larger than they need to be.
None of these show up in testing. All of them compound as you scale. A 48-hour code audit gives you a prioritised list of what to fix before they become user-visible problems — not after.
📋 Code Audit Quick Checklist
Use this as a starting framework for what any quality software code audit should examine:
- Security: Dependency vulnerabilities, authentication flows, input validation, secrets management
- Architecture: Service boundaries, coupling, single points of failure, data flow
- Performance: Query efficiency, caching strategy, async vs. sync operations, asset delivery
- Test Coverage: Branch coverage, integration tests, critical path coverage
- Maintainability: Documentation, code complexity scores, adherence to coding standards
- Scalability: Horizontal scaling readiness, stateless design, rate limiting, load handling
Who Actually Needs a 48-Hour Code Audit?
The honest answer is: most software teams. But there are specific situations where the ROI becomes immediate and undeniable.
You inherited a codebase. New CTO, new engineering lead, acquired company, or a vendor handover; you now own software you didn’t build. An audit is the fastest way to understand what you’ve actually inherited before you commit to a roadmap.
Your app has stopped scaling. If performance was fine at launch but has degraded as your user base has grown, the cause is almost certainly in the architecture, not the infrastructure. An audit finds it faster than weeks of internal investigation.
You’re approaching a funding round or M&A event. Sophisticated investors and acquirers now conduct technical due diligence as a matter of course. Knowing what they’ll find before they find it is simply smart preparation.
You’ve had a security incident. Or you’re worried you’re about to have one. A software rescue services engagement often starts with a code audit to establish exactly what was compromised and what else might be at risk.
Your team velocity has slowed significantly. When features that used to take a week now take a month, technical debt is almost always the culprit. An audit quantifies it and prioritises where to attack first.
Is Your Codebase Holding Your Business Back?
Our senior engineers will assess your application’s security, architecture, and scalability — and give you an honest picture of what you’re working with. No jargon. No sales pitch. Just clear findings and a practical path forward.
What the Audit Process Actually Looks Like
A proper 48-hour code audit isn’t just a senior developer glancing at your repo and writing up some notes. It’s a structured process with defined outputs.
Hour 0–4: Scoping and Access
The audit team needs access to your repository, CI/CD pipeline configuration, infrastructure diagrams (if they exist), and ideally a brief session with one of your senior engineers to understand the context. What’s the history of the system? Where are the known pain points? What are you worried about?
This context matters. Auditors who don’t understand the business logic behind your system will produce generic findings. The ones who do will tell you not just what’s wrong, but why it matters.
Hour 4–24: Deep Technical Analysis
This is where the actual work happens. Static analysis tools run across the codebase. Dependency trees are mapped and compared against known vulnerability databases. Architecture is diagrammed. Query patterns are reviewed. Authentication and authorisation logic is traced.
Experienced auditors will simultaneously flag quick wins (i.e. low-effort, high-impact fixes) and deeper structural issues that require a more considered remediation plan.
Hour 24–48: Synthesis and Reporting
Good audit output isn’t a 200-page PDF. It’s a prioritised finding set, categorised by severity, with clear remediation guidance for each issue. The deliverable should be something your engineering team can act on immediately and not something that requires another consultant to interpret.
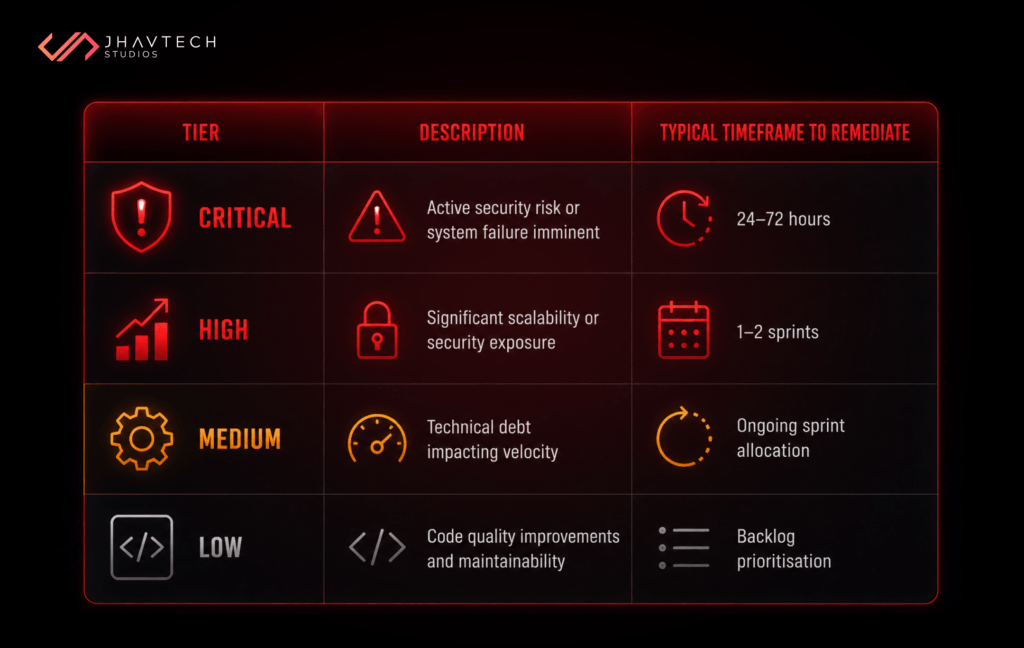
Findings should be tiered:
The Real Cost of Not Auditing
Here’s a framing that tends to land with engineering leadership and CFOs alike.
In the US alone, technical debt costs $2.41 trillion a year and would require $1.52 trillion to fix. The ratio is telling: the cost of carrying the debt is significantly higher than the cost of resolving it. Every year you don’t address it, you’re paying interest.
Since 2020, the average time to fix security flaws has increased by 47%. Teams simply can’t keep up with the scale of flaws being created.
The longer you wait, the harder and more expensive it gets. A problem that takes two sprints to fix today might take six sprints to fix in eighteen months when it’s had time to become load-bearing. This is the compounding nature of technical debt, and it’s exactly what Gartner, McKinsey, Deloitte, and Accenture have all documented independently in their research.
The 48-hour code audit is not a luxury. For any software business past the MVP stage, it’s maintenance. The same way you wouldn’t drive a vehicle for three years without a service, you shouldn’t run a production application for that long without an independent technical health check.
How a Code Audit Connects to Software Rescue
Sometimes an audit confirms what you suspected: things are manageable, a few priority fixes will get you back on track, and your team can handle the remediation with some guidance.
But sometimes it reveals something more serious — a system so burdened by architectural debt, security exposure, and legacy dependencies that incremental fixes won’t cut it. That’s when you need a team that can step in, stabilise what’s broken, and rebuild what isn’t salvageable.
A rescue engagement picks up where the audit leaves off. Rather than patching around the problems, a rescue team works alongside (or in some cases, temporarily substitutes for) your internal team to stabilise the application, address critical risks, and build a sustainable forward path. The audit is the diagnosis; the rescue is the surgery.
If you’ve read our breakdown of why apps stop scaling under real-world load, you’ll recognise the pattern. Most software projects don’t fail catastrophically all at once. They fail slowly, through accumulated decisions that seemed reasonable at the time and become untenable at scale.
The 48-hour code audit catches that trajectory early enough to change it.
Getting the Most Out of Your Audit
If you’re commissioning a code audit (internal or external), a few things will determine whether you get genuinely useful output or a generic report:
- Choose auditors who’ve built production systems, not just reviewed them. The ability to distinguish between a theoretical concern and an actual operational risk comes from experience shipping software.
- Don’t sanitise access before the audit. Some teams are tempted to tidy up the repo before external eyes see it. Don’t. The audit should see the real system, not a curated version of it.
- Brief the auditors on business context. A payment processing module deserves different scrutiny than a marketing content API. Auditors who understand the business stakes will prioritise more effectively.
- Allocate engineering time to act on findings. An audit that produces a report nobody has time to act on is a waste. Build the remediation capacity before you commission the work.
Ready to Know What’s Actually in Your Codebase?
Our team has rescued dozens of production applications from the consequences of unaddressed technical debt, security vulnerabilities, and architectural shortcuts. We’ll tell you what we find clearly, practically, and without the jargon.
Frequently Asked Questions
What exactly happens during a 48-hour code audit?
An external engineering team reviews your codebase using static analysis tools and manual inspection, covering security, architecture, test coverage, and performance. The output is a prioritised findings report your team can act on straight away. The 48-hour figure reflects the audit team’s working effort. Delivery may span two to four calendar days.
How is a 48-hour code audit different from a regular internal code review?
Internal reviews are narrow. They focus on individual pull requests. A 48-hour audit is systemic: it examines the entire codebase with independent eyes that have no stake in the decisions that were made. That independence is what makes findings credible and actionable.
How much does a software code audit typically cost?
It depends on codebase size and complexity. Jhavtech Studios offers a free initial code review so you know what a full audit involves before committing to anything. The better question: what does a serious security breach or six months of compounding technical debt actually cost your business?
What should I do with the audit findings?
Fix critical security issues within days, not sprints. Schedule high-severity architectural fixes in your next one to two release cycles. Fold medium and low findings into your regular technical debt allocation — typically 15–20% of engineering capacity. If the volume is overwhelming, a dedicated rescue engagement is faster than tackling it incrementally while still shipping.
Can a 48-hour code audit be done on a mobile app?
Yes. The process is the same, with platform-specific checks for React Native, Flutter, Swift, and Kotlin codebases. Auditors also examine the backend API layer, where the majority of mobile app security vulnerabilities actually live.
.svg)